
























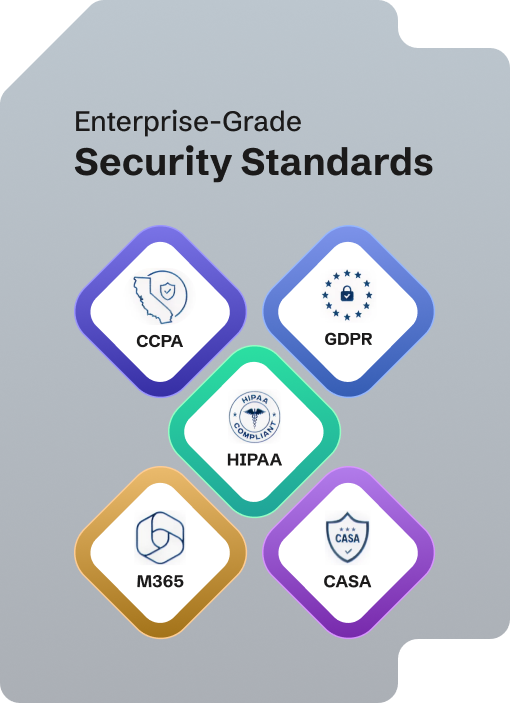
Risk is engineered down from day one: role-based access, guardrails, human-in-the-loop for sensitive actions, and an incident-response playbook.
Models are tested before launch and continuously in production for quality, bias, and cost/latency.
Collect only what’s needed, encrypt everywhere, and control access tightly. Data residency options, retention policies, and full audit logs ensure compliance and user trust.
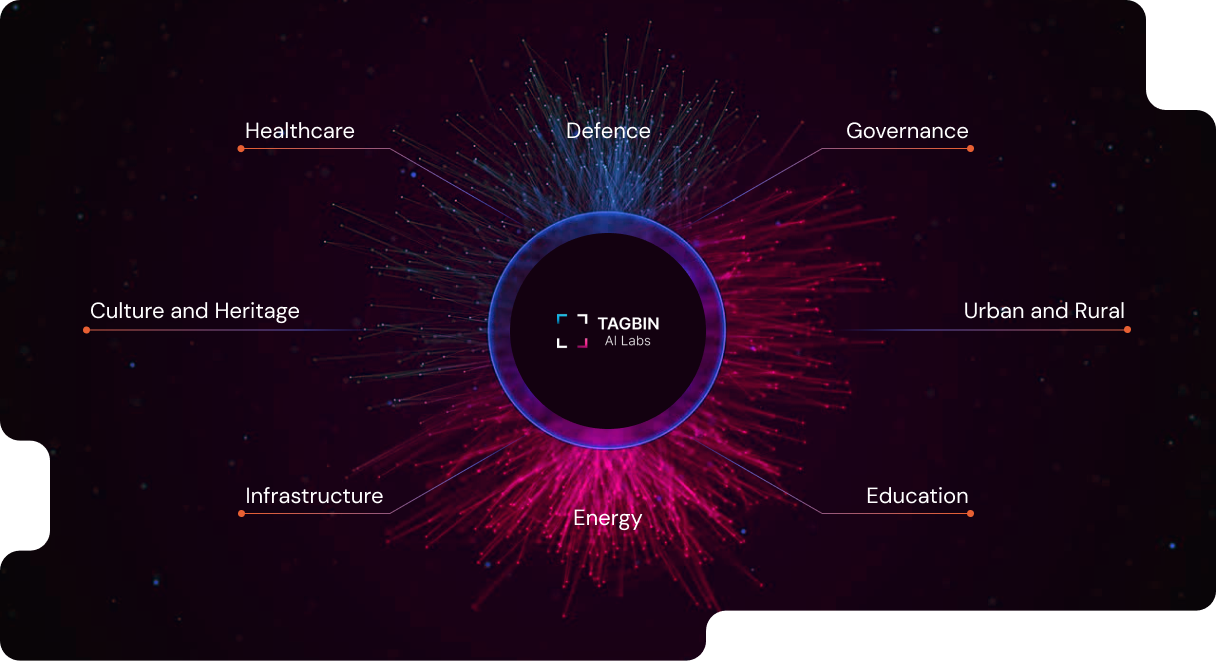
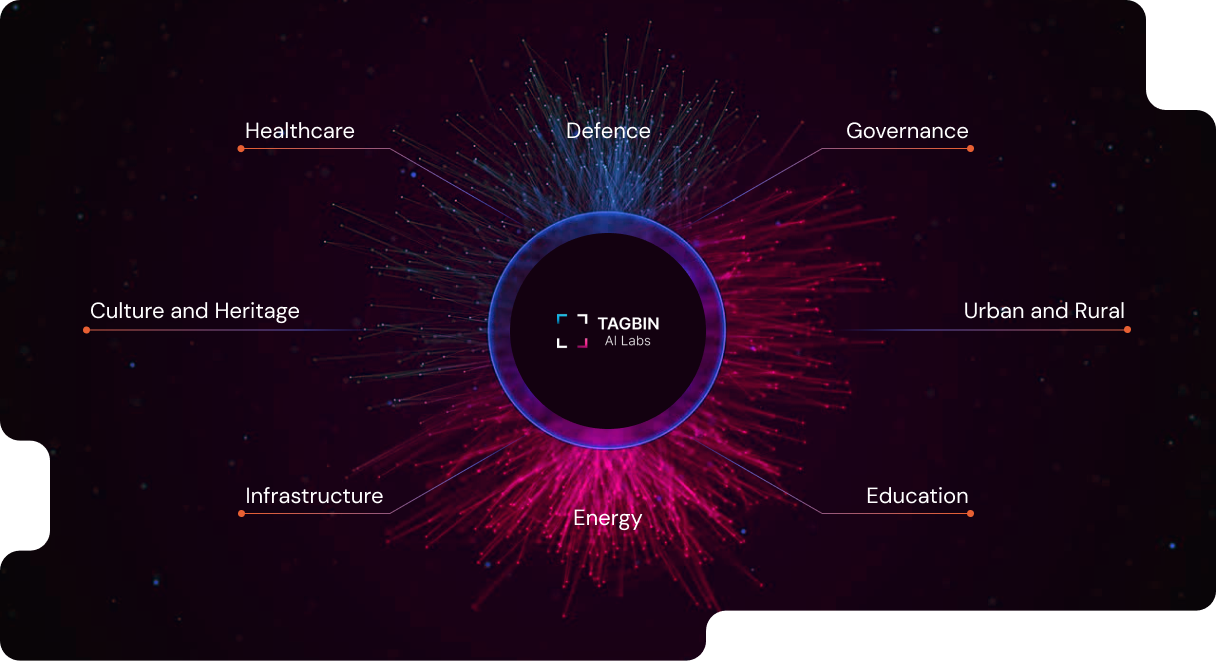
From back office to boardroom, we turn organizations into learning systems—automating the ordinary, surfacing the urgent, and converting information into outcomes that compound over time.
Data sources/APIs (grievances, assets, sensors, GIS), alert rules, user roles, and incident workflows you already follow.
We support both on-premise and cloud. Data can stay in your data center or India-region cloud with residency controls.
Yes admin/user training, SOPs, and SLA-backed support with ongoing monitoring and updates.